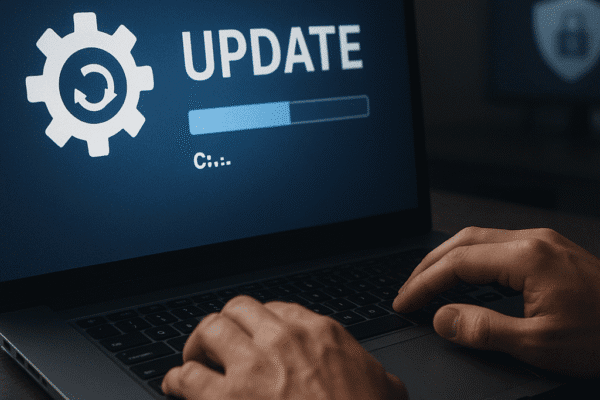
The Importance of Security Patch Management
Effective security patch management forms the backbone of a resilient business security strategy. Organizations are constantly facing an evolving threat landscape where unpatched software can serve as an entry point for cybercriminals. This article explores the essential practices, common challenges, and strategic approaches to ensure that your enterprise consistently applies critical updates, minimizes vulnerabilities, and strengthens its operational integrity. Understanding the Patch Management Lifecycle Successful patch management involves a series…