How to Prevent Security Incidents in Shared Office Buildings
Shared office buildings present a complex environment where several companies operate under one roof, sharing facilities, utilities, and common areas. Establishing a robust security posture is critical to safeguard assets, protect sensitive data, and maintain a safe workplace for all tenants. This article outlines best practices to prevent security incidents in shared office environments, focusing on risk assessment, physical and digital safeguards, and employee preparedness. Risk Assessment and Access Control…
How to Use Predictive Analytics in Workplace Safety
Organizations increasingly rely on data to protect employees and assets. By leveraging predictive analytics, companies can anticipate potential hazards and implement timely controls, transforming traditional safety protocols into proactive strategies. Embracing a data-driven approach not only reduces workplace incidents but also enhances operational efficiency and fosters a culture of continuous improvement. Importance of Predictive Analytics in Workplace Safety Traditional safety programs often react to incidents after they occur. In contrast,…

How to Secure Company-Owned Mobile Phones
Securing company-owned mobile phones demands a comprehensive strategy that balances user convenience with robust protection against evolving cyber threats. A well-structured approach encompasses clear governance, advanced technical controls, and continuous oversight. By integrating policies that reflect organizational risk appetite, deploying a capable MDM solution, and enforcing strong authentication mechanisms, businesses can mitigate data breaches and unauthorized access. Prioritizing encryption for data at rest and in transit, alongside proactive monitoring and…
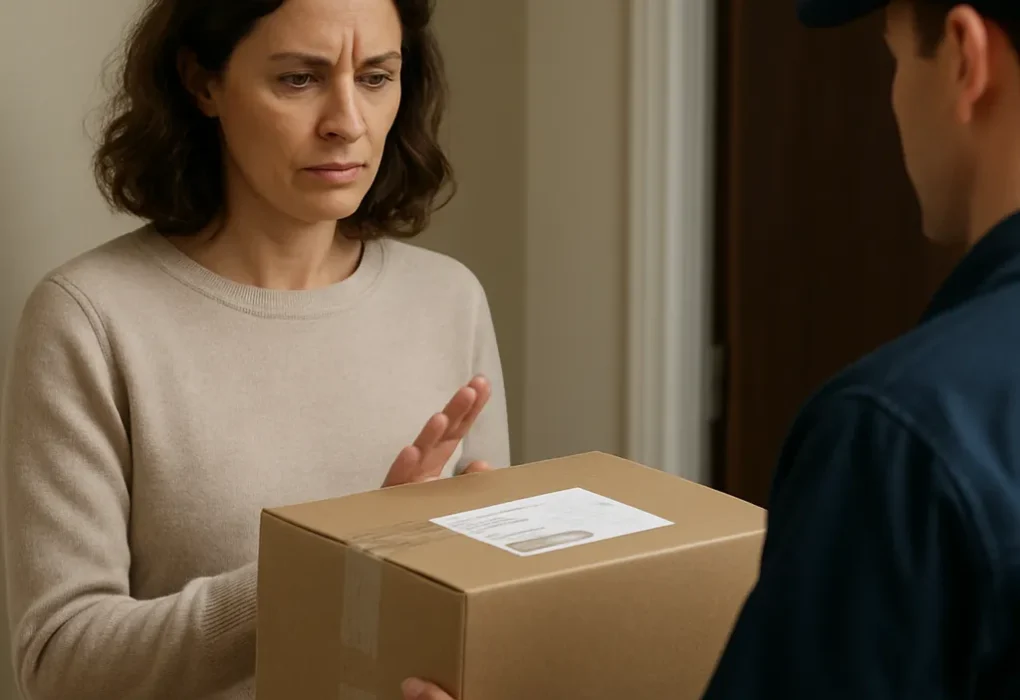
How to Handle Suspicious Deliveries and Mail Security
Businesses encounter a wide spectrum of security challenges, and one of the most overlooked yet potentially devastating risks comes through the mailroom. Suspicious parcels or letters can contain explosives, biological agents, or other hazards that threaten personnel, property, and continuity of operations. Developing a comprehensive mail security framework not only safeguards employees but also reinforces your organization’s resilience and compliance posture. The following chapters delve into practical strategies for recognition,…

How to Maintain Safety in Warehouse Logistics Operations
Ensuring the integrity of warehouse logistics operations requires meticulous planning and ongoing safety measures. From initial site design to day-to-day routines, every component plays a crucial role in protecting personnel, assets, and the supply chain’s overall efficiency. Below are strategic approaches to maintain a secure and productive warehouse environment. Risk Assessment and Site Organization Identifying Potential Hazards Conduct comprehensive audits to catalog risks such as slip-and-fall zones, falling objects, or…

How to Protect Your Company from Credential Stuffing Attacks
Credential stuffing represents a formidable challenge for modern businesses as attackers exploit stolen credentials to access corporate systems. By automating login attempts with vast lists of username–password pairs, cybercriminals can bypass weak defenses and compromise sensitive data. This article explores practical strategies to safeguard your organization against these threats while reinforcing overall security posture. Understanding Credential Stuffing Attacks Credential stuffing relies on two fundamental elements: a database of stolen login…

How to Secure APIs in Business Applications
Securing APIs in modern business applications is critical to protect sensitive data, maintain system integrity, and uphold customer trust. With the rise of cloud services and microservices, APIs serve as the backbone of digital ecosystems, enabling seamless integration between internal systems and external partners. However, this connectivity also introduces potential vulnerability points that can be exploited by malicious actors. Implementing a robust API security strategy requires a multifaceted approach, covering…
How to Safely Dispose of Confidential Paper Documents
Handling sensitive paperwork in a corporate environment demands a strategic approach to avoid data breaches and preserve reputational integrity. Businesses must adopt a comprehensive set of practices that range from accurate document classification to collaboration with trusted disposal vendors. This article explores effective techniques for the secure destruction of confidential paper documents, addresses relevant compliance frameworks and offers guidance on policy implementation to keep organizational data safe. Proper Assessment of…

How to Identify Vulnerabilities Through Regular Assessments
Organizations that prioritize cybersecurity often discover that consistent evaluation of their infrastructure uncovers hidden risks long before they escalate. By embedding regular assessments into operational workflows, businesses establish a systematic method for detecting and addressing vulnerabilities. This proactive stance not only safeguards sensitive data but also aligns with industry compliance mandates and builds stakeholder trust. Understanding the Role of Regular Security Assessments At its core, a security assessment is a…

How to Protect Confidential Boardroom Discussions
Protecting the privacy of executive-level conversations goes beyond locked doors and non-disclosure agreements. Boardroom discussions often involve sensitive data on mergers, financial performance, and strategic pivots. Any slip can expose an organization to competitive harm, legal liabilities, or reputational damage. This article explores practical measures to secure these high-stakes deliberations and ensure that only authorized individuals participate in and retain critical information. Boardroom Threat Landscape The modern corporate governance environment…