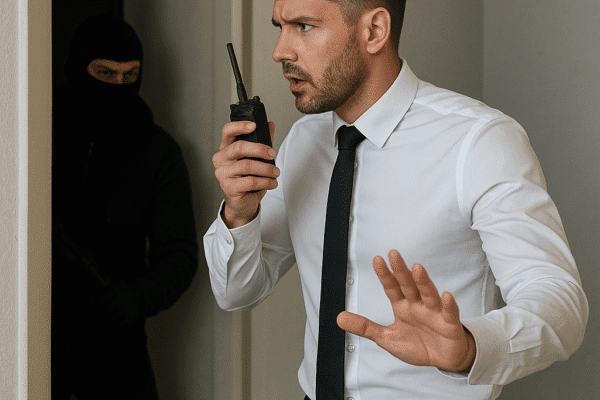
How to Respond to a Physical Security Breach
Reacting swiftly and effectively to a physical security breach is essential for protecting assets, personnel, and reputation. This article outlines practical strategies and detailed procedures for organizations to prepare, respond, and recover from unauthorized access or other breaches. Preparation Strategies for Physical Security Robust preparation forms the foundation of any successful response to a breach. By establishing strong protocols, continuous monitoring, and regular training, organizations can reduce both the likelihood…